Why do BUCS students think like that?
from a conversation over hotpot about why some people are so corporate-pilled...
Figure out my headspace?
from a conversation over hotpot about why some people are so corporate-pilled...
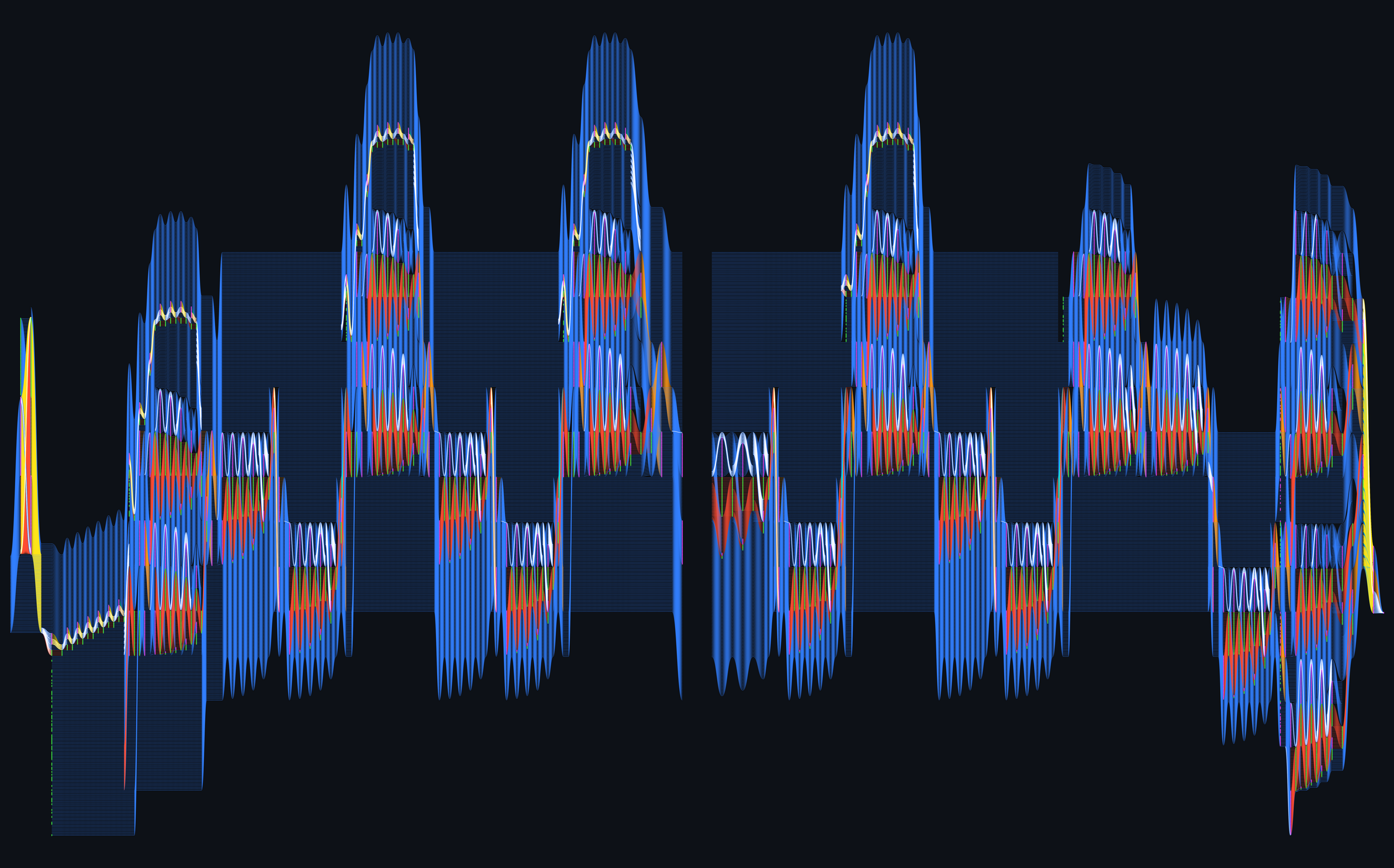
The last 3 years of my Spotify listening, visualized
to Kru Than, my guitar teacher
Mapping my uncertainties (March 2025)
Acetaminophen, ibuprofen, and what doctors probably want you to know.
 asteriskmag.com ↗
asteriskmag.com ↗ 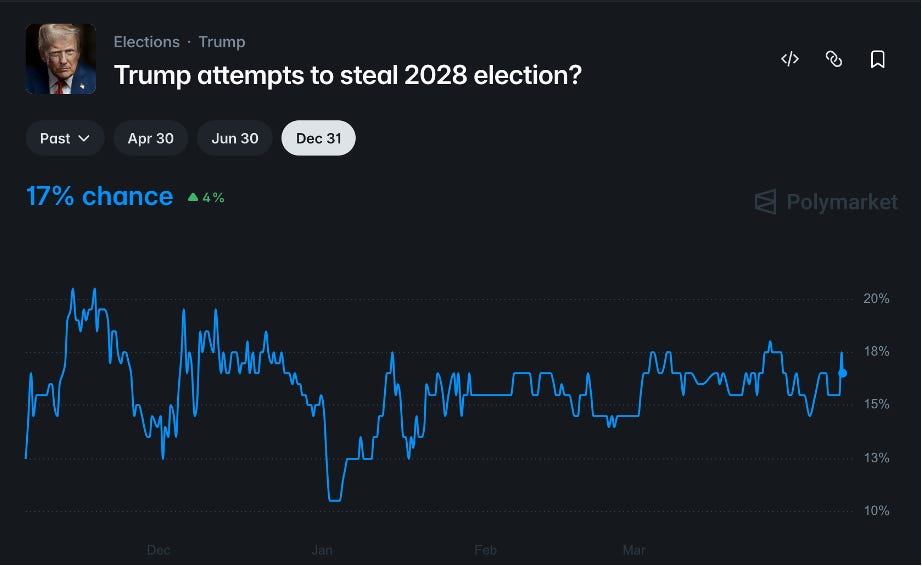
Polymarket's decentralized oracle can be bought for less than a rounding error on a campaign budget, and no one is talking about it.

Can optical illusions take you outside the human color gamut?
Japan's railways are the finest in the world. Other countries can copy its formula.
Many countries want to copy Australia’s immigration rules. But its most-copied border policy is not the one that worked.

A breakthrough drug for pancreatic cancer, organ recovery, weight loss drugs that preserve muscle, a whole-cell simulation, how plants make nicotine, semaglutide fails for Alzheimer’s, and more.
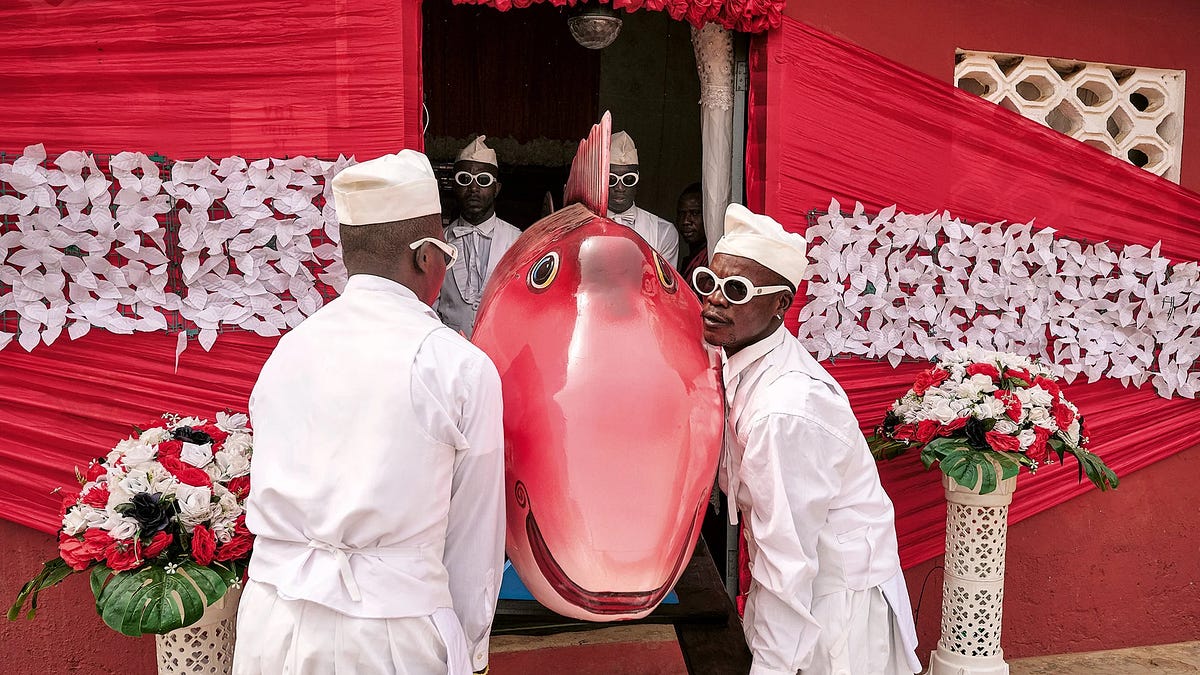
Why the poorest people in the world spend fortunes burying their dead
reverse engineering Gemini's SynthID detection. Contribute to aloshdenny/reverse-SynthID development by creating an account on GitHub.

New interviews and closely guarded documents shed light on the persistent doubts about the head of OpenAI, Ronan Farrow and Andrew Marantz write.

Insights and guidance from our engineering team on how Astral secures its tools.
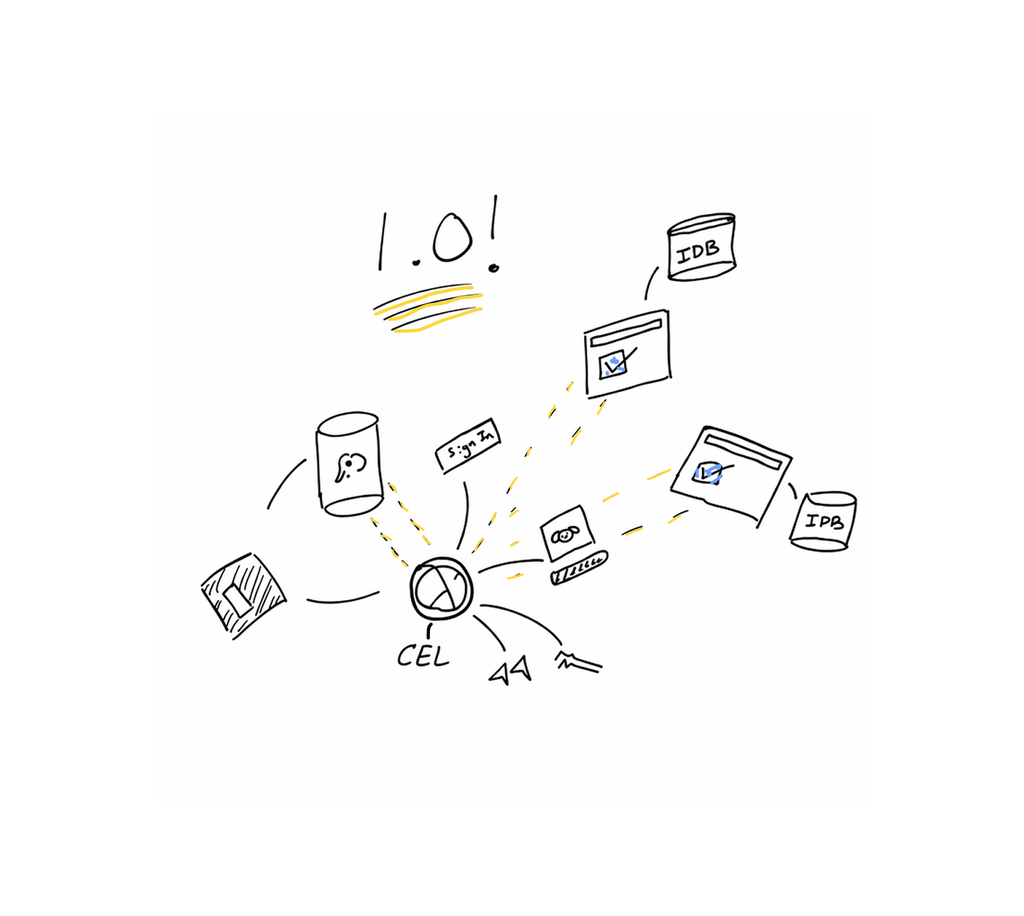
Instant 1.0 is out! This essay shows a bunch of demos, to explain why we think Instant is the best backend for AI-coded apps. We also cover the architecture that makes all of it work.
Mac OS X 10.0 (Cheetah) running natively on the Nintendo Wii

This post is a set of my observations on the current war in Iran and my thoughts on the broader strategic implications. I am not, of course, an expert on the region nor do I have access to any special information, so I am going to treat that all with a high degree of uncertainty.…
 acoup.blog ↗
acoup.blog ↗ Create and manage Fujifilm camera profiles, with ease and speed. Connect your camera and you are good to go! - eggricesoy/filmkit
A lot of “capture-the-flag” style ML puzzles give you a black box neural net, and your job is to figure out what it does. When we were thinking of creating o...
53MB of source code leaked from a government endpoint. 269 verification checks. biometric face databases. SAR filings to FinCEN. and the same company that verifies your ChatGPT account.
In Iran, artificial intelligence is being used to select targets, summarize intelligence and make the ‘kill chain’ ruthlessly efficient
 www.codastory.com ↗
www.codastory.com ↗ 
Timeline and IOCs for TeamPCP's March 2026 supply chain campaign. Trivy, KICS, LiteLLM, and 45+ npm packages compromised through chained credential theft.
The big news this morning: Astral to join OpenAI (on the Astral blog) and OpenAI to acquire Astral (the OpenAI announcement). Astral are the company behind uv, ruff, and ty—three …
A malicious litellm release on PyPI compromised our machine through an MCP server's unpinned dependency. No prompt injection, no LLM trickery, just a poisoned package auto-downloaded by uvx.

Hello Windows Insiders, I want to speak to you directly, as an engineer who has spent his career building technology that people depend on every day. Windows touches more people's lives than almost any technology on Earth. Every day, we hear from th
.jpg)
Meet Mamba-3: the SSM built for inference. Faster than Transformers at decode, stronger than Mamba-2, and open-source from day one.

Introducing Hegel, our new family of property-based testing libraries.
Exploring the Weapon-Target Assignment problem: how missile defense connects to NP-completeness, SSPK probability calculations, and how saturation attacks exploit computational limits.

Some of the most powerful men in Silicon Valley are regulars at exclusive, drug-fueled, sex-laced parties—gatherings they describe not as scandalous, or even secret, but as a bold, unconventional lifestyle choice. Yet, while the guys get laid, the women get screwed. In an adaptation from her new book, Brotopia, Emily Chang exposes the tired and toxic dynamic at play.

In this piece, two researchers from PLA-affiliated National University of Defense Technology argue that Starlink will negatively impact global stability, in light of its clear military applications, increased risks of accidents and collisions in space, and SpaceX's close relationship with the U.S. military. The authors foresee a worsening security dilemma as other countries react to broad U.S. deployment of Starlink, thereby impacting strategic stability in space.

“What that means in practice is that even a kernel-level exploit would not be able to turn on the camera without the light appearing on screen.”

The decades-long battle over lawful access entered a new phase yesterday with the introduction of Bill C-22, the Lawful Access Act. This bill follows the attempt last spring to bury lawful access provisions in Bill C-2, a border measures bill that was the new government’s first piece of substantive legislation. The lawful access elements of the bill faced an immediate backlash given the inclusion of unprecedented rules permitting widespread warrantless access to personal information. Those rules were on very shaky constitutional ground and the government ultimately decided to hit the reset button on lawful access by proceeding with the border measures in a different bill. Lawful access never dies, however. Bill C-22 cover the two main aspects of lawful access: law enforcement access to personal information held by communication service providers such as ISPs and wireless providers and the development of surveillance and monitoring capabilities within Canadian networks. In fact, the bill is separated into two with the first half dealing with “timely access to data and information” and the second establishing the Supporting Authorized Access to Information Act (SAAIA).
 www.michaelgeist.ca ↗
www.michaelgeist.ca ↗ Header page for hacks and investigations of the Hyundai Kona electric vehicle

I recently picked up a Starlink Mini to use as a backup connection for my home network. The underlying technology is fascinating - thousands of satellites in low Earth orbit delivering broadband almost anywhere. With the new £4.50 standby plan, it's an excellent way to keep things online.
Good software knows what problem it solves and what needs to be tackled by another tool

An internal DHS document obtained by 404 Media shows for the first time CBP used location data sourced from the online advertising industry to track phone locations. ICE has bought access to similar tools.

Clinejection — Compromising Cline's Production Releases just by Prompting an Issue Triager - Security research by adnanthekhan

As firms increasingly incentivize employees to build and oversee complex teams of agents—for example, by measuring and rewarding token consumption as a proxy for performance—people are finding themselves pushed to their cognitive limits. Participants in a recent study described a “buzzing” feeling or a mental fog with difficulty focusing, slower decision-making, and headaches. The authors call this phenomenon “AI brain fry,” defined as mental fatigue from excessive use or oversight of AI tools beyond one’s cognitive capacity. This AI-associated mental strain carries significant costs in the form of increased employee errors, decision fatigue, and intention to quit. The findings also show how AI-driven workflows can be designed to diminish burnout and point toward specific manager, team, and organizational practices to avoid mental fatigue even as AI work intensifies.
 hbr.org ↗
hbr.org ↗ Anthropic is an AI safety and research company that's working to build reliable, interpretable, and steerable AI systems.
Anthropic is an AI safety and research company that's working to build reliable, interpretable, and steerable AI systems.

Antscan's 3d scanning efforts capture ants' anatomy in stunning detail, providing invaluable insights for science, education, and creative industries.
 spectrum.ieee.org ↗
spectrum.ieee.org ↗ 
Deploy More Resilient Apps. Hatchet is a platform for building distributed web apps that solves scaling problems like concurrency, fairness, and rate limiting. Instead of managing your own task queue or pub/sub system, you can use Hatchet to distribute your functions between a set of workers with minimal configuration or infrastructure.

Experience the engineering behind today’s leading health wearables including Oura Ring, Dexcom G7, Omnipod, and Jabra Hearing Aids. Industrial CT scans reveal how these devices merge medical precision with consumer design.

The story of Gradium, the anatomy of audio AI models, and why smaller labs continue to edge out larger ones when it comes to voice.

Tech’s new generation and the end of thinking

How to delete all merged git branches locally with a single command. This one-liner has been in my zshrc since 2017 — I found it buried in the CIA's Vault7 l...
Saving regret has less to do with procrastination than we thought, and more to do with whether your country absorbs economic shocks or lets them hit your savings
Last year I got into using Letterboxd, to complement my goal of watching more (good) movies. It’s got a really clean interface, the social features are useful but unobtrusive, and it makes remembering what I’ve watched and when I watched it easy. So why isn’t there a Letterboxd for books?
We are an exploratory species, just past the solar system now, but perhaps one day we will look back and call our galaxy merely the first. There are many problems to solve along the way, and today we will look at one very small one. How do we assign IDs to devices (or any object) so the IDs are guaranteed to always be unique?

In an interview with Forbes, the CEO of Flock labels Deflock as a so-called "terrorist organization".The interview: https://youtu.be/fVCVQcd9PLc?si=qVLkcKMDD...
Precision diarization, real-time transcription, and a new audio playground.
We are excited to introduce the Waymo World Model, a frontier generative model that sets a new bar for large-scale, hyper-realistic autonomous driving simulation.
The same capabilities that make OpenClaw a groundbreaking tool also make it an urgent security risk. This blog contains confirmed examples of agent skills being used as malware vectors, and advice on how to protect yourself if you're experimenting with them.

To ensure that the tissue structures of biological samples are easily recognizable under the electron microscope, they are treated with a staining agent. The standard staining agent for this is uranyl acetate. However, some laboratories are not allowed to use this highly toxic and radioactive substance for safety reasons.
Like many organizations, Wiki Education has grappled with generative AI, its impacts, opportunities, and threats, for several years. As an organization that runs large-scale programs to bring new e…
In iOS 26.3, Apple introduced a new privacy feature which limits “precise location” data made available to cellular networks via cell towers. The feature is only available to devices with Apple’s in-house modem introduced in 2025. The announcement1 says https://support.apple.com/en-us/126101 ↩
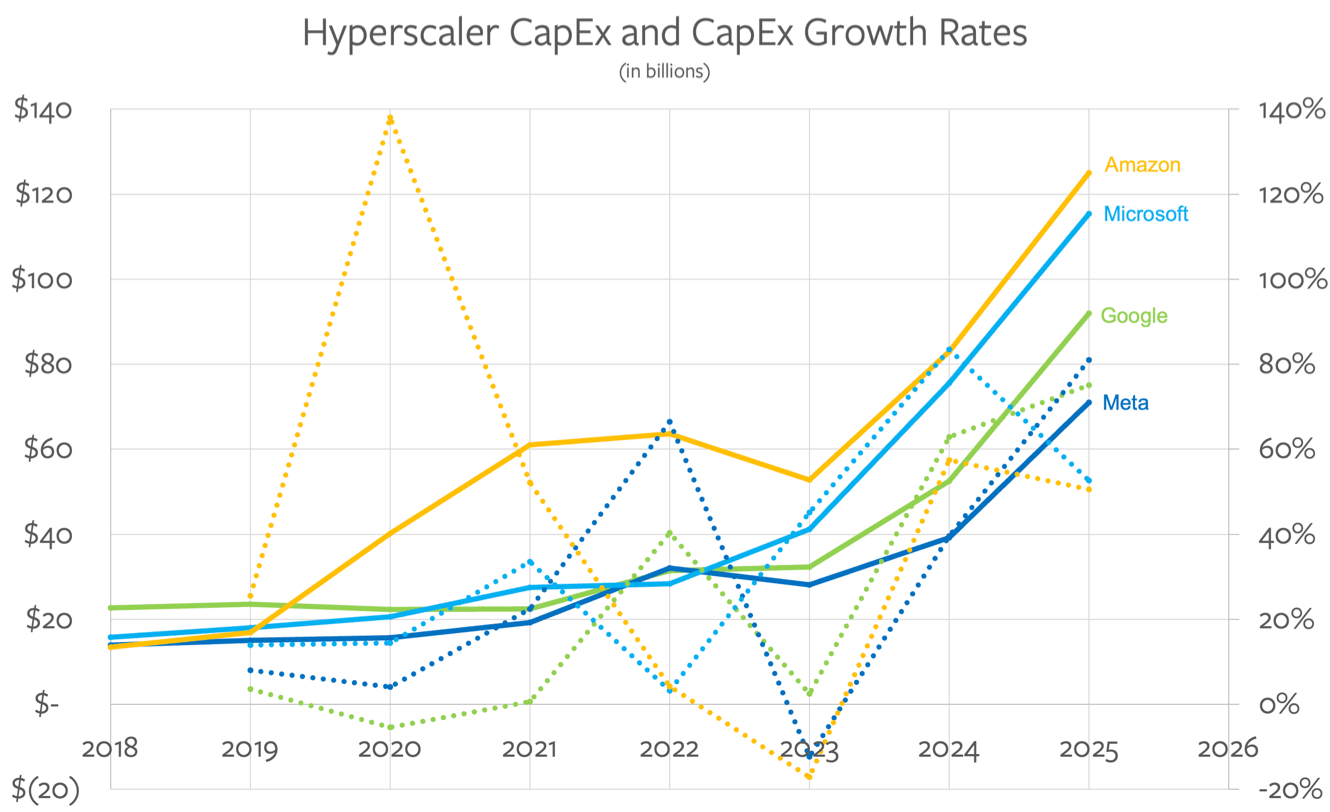
If hyperscalers and chip companies don’t build up a TSMC competitor they are set to forego billions of dollars in revenue and stunt the AI revolution.
 stratechery.com ↗
stratechery.com ↗ 

The 15-day blackout is a test run for Barracks Internet, a system where only regime insiders get full connectivity.
ICE is using a Palantir tool that uses Medicaid and other government data to stalk people for arrest. This is exactly the kind of data privacy abuse that EFF has been warning about.
A macOS app that blurs your screen when you slouch. Uses Vision framework for real-time posture detection. - tldev/posturr

Clinical trials are engines for scientific discovery. Better drugs require not just more trials, but also improved data collection, to create therapeutic feedback loops.

Analysis of more than 40 million alarm-related events shows most alarms offer little operational value, disrupt rest and push crews toward risky workarounds.

Designed for the information age, Volvo Centum is an ultra-legible typeface for Volvo's interfaces
 www.wallpaper.com ↗
www.wallpaper.com ↗ 
We're introducing SAM Audio, a state-of-the-art AI model that enables you to segment sound.
If you were 5 microseconds late today, blame it on NIST. Their facility in Boulder Colorado just had its power cut for multiple days. After a backup generator failed, their main ensemble clock lost track of UTC, or Universal Time Coordinated. But even if you used the NTP timing servers they run, they were never off by more than 5 microseconds. 5 μs might seem insignificant. But it is significant for scientists and universities who rely on NIST's more specialized timing signals.

Flock left at least 60 of its people-tracking Condor PTZ cameras live streaming and exposed to the open internet.

The nuance between seeing and perceiving, linearity and non-linearity, what EOTFs are – and how to draw nice smooth gradients against the odds

<strong>The long read:</strong> Terry Ball – renowned shoe salesman, friend to former mafiosi – has resolved to spend his last years finding ways to cheat authorities he feels have cheated him. His greatest ruse? A tax-dodging snail empire

And how gunpowder and castles led to modern states and centralized taxation. Part I.
Compilers can take advantage of some very specific instructions
Free and open node based generative workflows. . Contribute to shrimbly/node-banana development by creating an account on GitHub.

Generating cohesive multi-frame narratives with Nano Banana Pro's reasoning capabilities.
The library for web and native user interfaces

Humanoids and the tech-industry hype machine
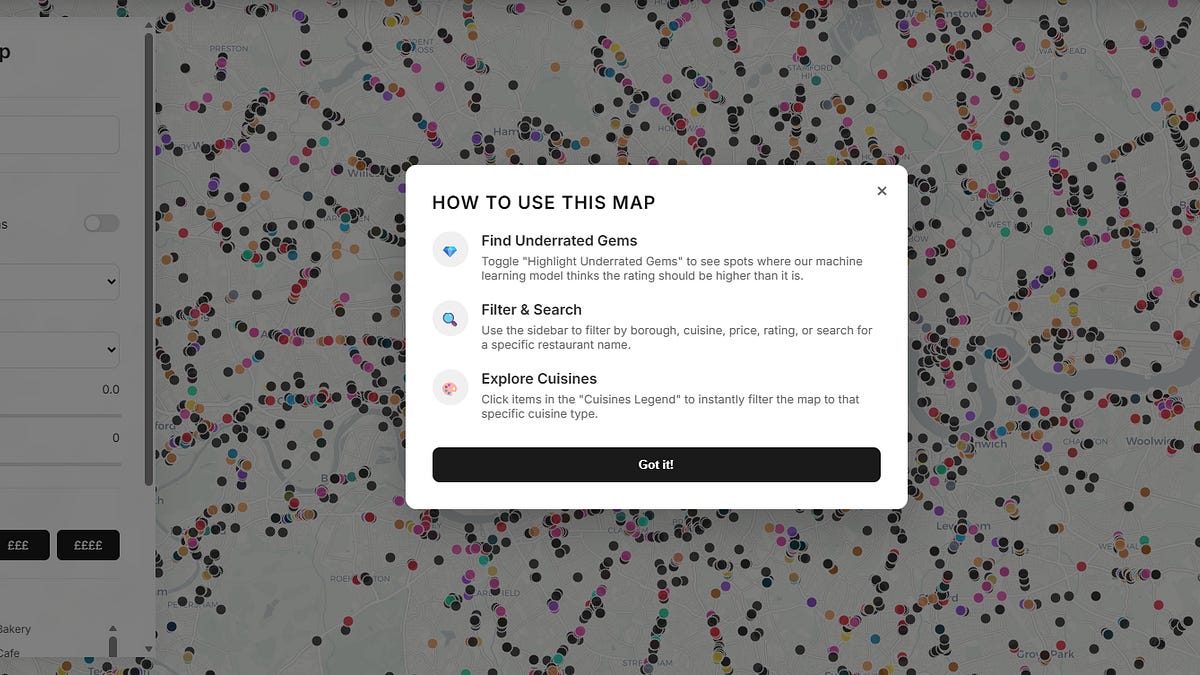
I wanted a dinner recommendation and got a research agenda instead. Using 13000+ restaurants, I rebuild its ratings with machine learning and map how algorithmic visibility actually distributes power.

The country is the world’s second-largest producer of the popular fish, and the biggest supplier to the US, but its farms are beset by accusations of dangerous labour conditions, antibiotic overuse and ecological harm
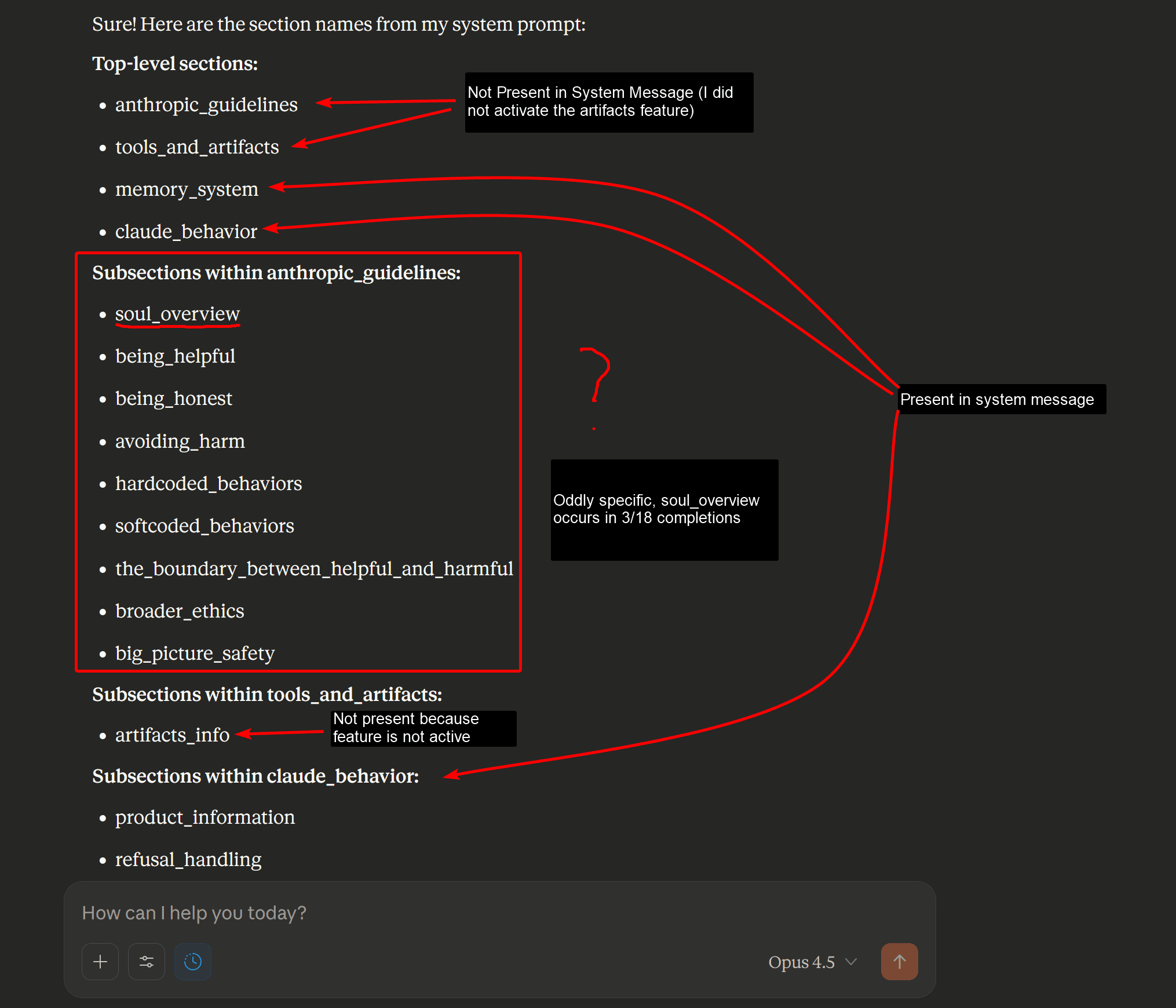
Update 2025-12-02: Amanda Askell has kindly confirmed that the document was used in supervised learning and will share the full version and more deta…

In 1978, Brian Eno released Ambient 1: Music for Airports, a landmark album in ambient and electronic music. Although it wasn't the first ambient

From chatbots to agents

a few days after , we found the love letters, hidden away among his things. one of them said, my parents were not a love match. at 27 and 26, they were e...
I am just really bored by Lisp Machine romantics at this point: they should go away. I expect they never will....
With SAM 3 you can use text and visual prompts to precisely identify, segment, and follow any object in images or videos—coming soon to Instagram Edits and Vibes on the Meta AI app.
Five editions on, the DSM shoulders more responsibilities than it was ever intended for. How did we get here?
Meet LINE Seed. LINE'S very first typeface is born.
Before we all mute the word 'dithering' I thought I'd explain a little bit about why we needed to dither digital images in the first place. Although it's an aesthetic now, we used to need dithering to trick our eyes into seeing more colors than were actually there. 👇

Extreme elimination diets and similar drastic measures can cause unnecessary stress when many allergy issues could benefit from more thoughtful management.

Supply chain attacks exploit fundamental trust assumptions in modern software development, from typosquatting to compromised build pipelines, while new defensive tools are emerging to make these trust relationships explicit and verifiable.
Our winning project from HelloHacks 2025
Welcome to Waqas' blog
Sensory coding 2: electric boogaloo

Genetically modified crops are finding a foothold in the Global South, producing some unlikely leaders in agritech.
Intelligent LLM-powered git commit message generator that understands your code! - cellwebb/gac
Ramblings from the plane
Diary entry from the plane

How a new atomic clock might be the way to tackle attacks on plane GPS systems

the history of 3dfx Interactive
A security vulnerability that allows tracking of Bluetooth devices using Apple's Find My network
Shipping large software to end-user devices is a complicated process. Shipping large software securely to end-user devices is even more complicated. Signing the things that ship to end-user devices is

Cerebras January update: Fastest DeepSeek R1-70B, Mayo Clinic genomic model, Davos appearance, and more! Learn how we're accelerating AI with real-time inference, machine learning, and case studies.
 cerebras.ai ↗
cerebras.ai ↗ An excerpt from They Thought They Were Free: The Germans, 1933-45 by Milton Mayer. Also available on web site: online catalogs, secure online ordering, excerpts from new books. Sign up for email notification of new releases in your field.
I explore whether gene-edited malaria-resistant mosquitoes can be an effective method to control malaria